Understanding Cryptography: Essential Concepts for Blockchain Security

What is Cryptography?
Cryptography represents a fundamental pillar of modern digital security, addressing the growing concerns about online privacy and data protection in an increasingly interconnected world. As cyber threats continue to evolve and more individuals rely on digital services for their daily activities, understanding cryptography in computer networks becomes essential for comprehending how our sensitive information remains secure in the digital age.
What is Cryptography?
Cryptography is the science and practice of secure communication between parties in the presence of potential adversaries. The term itself derives from Greek roots meaning "hidden writing," which accurately reflects its primary purpose. At its core, cryptography in computer networks focuses on designing systems that enable individuals to transmit, receive, and interpret sensitive information without unauthorized third parties accessing or understanding the content.
The foundation of cryptographic communication rests on two essential elements: plaintext and ciphertext. Plaintext represents the original, readable message in a natural language that the sender wishes to communicate. Ciphertext, conversely, is the transformed version of the plaintext that appears as unintelligible data to anyone without the proper decoding mechanism. For example, a simple message like "I love you" might be converted into a numerical sequence "0912152205251521," where each letter corresponds to its position in the alphabet. This transformation process is known as encryption, while the reverse process of converting ciphertext back to its original plaintext form is called decryption. The effectiveness of this system relies on both parties knowing the encryption method, enabling secure communication even across unsecured channels in computer networks.
A Brief Overview of Encryption's History
The history of cryptography extends far beyond the digital age, with documented use dating back thousands of years. One of the most famous early examples comes from Julius Caesar, who developed the Caesar cipher for military communications. This technique involved shifting each letter of the alphabet by three positions, creating what is known as a substitution cipher. Archaeological evidence suggests even earlier use of cryptographic techniques, with unusual hieroglyphics found in Egyptian tombs potentially representing some of humanity's first attempts at encoded communication.
Throughout history, governments and notable figures have employed increasingly sophisticated encryption methods. In the 16th century, Mary Queen of Scots and her supporter Anthony Babington used an elaborate code system featuring 23 symbols representing certain letters, 25 symbols for complete words, and several meaningless decoy symbols. However, Sir Francis Walsingham's cryptanalysis team successfully deciphered these messages, uncovering an assassination plot against Queen Elizabeth I, which ultimately led to Mary's execution in 1587.
The 20th century witnessed remarkable advances in cryptographic technology, particularly during World War II. Nazi Germany developed the Enigma machine, a sophisticated encryption device using multiple rotors to scramble messages, with daily changes to the circuit system making unauthorized decryption virtually impossible. British mathematician Alan Turing's creation of the Bombe machine proved instrumental in cracking Enigma codes, significantly contributing to the Allied victory. Following the war, cryptography evolved from physical encoding devices to software-based systems. IBM's introduction of the Data Encryption Software (DES) in 1977, developed in collaboration with the NSA, established the standard for computer encryption. As computing power increased, the need for stronger encryption led to the development of the Advanced Encryption Standard (AES), which remains the cornerstone of modern digital security and cryptography in computer networks today.
What is a Key in Cryptography?
The concept of a cryptographic key is fundamental to understanding how encryption and decryption processes function in computer networks. A key serves as the essential tool that allows authorized parties to unlock the meaning of encrypted messages. In historical contexts, the key referred to the specific cipher method or pattern used to encode information. For instance, once Walsingham's team discovered the symbol system in Babington's correspondence, they possessed the key to decrypt all related communications.
In contemporary digital systems, keys have evolved into complex alphanumeric sequences that work in conjunction with sophisticated algorithms to transform plaintext into ciphertext and vice versa. These digital keys function as virtual tools that enable secure data transmission between trusted parties while preventing unauthorized access across computer networks. The length and complexity of modern cryptographic keys significantly enhance security, making it computationally infeasible for attackers to decrypt messages through brute force methods. The security of any cryptographic system fundamentally depends on the secrecy and proper management of these keys.
Two Major Types of Cryptography
Modern cryptographic systems employ keys in two distinct methodologies, each with unique characteristics and applications in computer networks.
Symmetric key cryptography represents the traditional approach to encryption, predating advanced computer systems. This method uses a single key for both encryption and decryption operations. Both the sender and receiver must possess access to this shared key to successfully protect and read encrypted messages. The Advanced Encryption Standard (AES) exemplifies symmetric encryption, breaking data into 128-bit blocks and using keys of 128, 192, or 256 bits to encrypt and decrypt information. While symmetric encryption offers computational efficiency and speed, it presents challenges in key distribution, as both parties must securely exchange the shared key before communication can begin across computer networks.
Asymmetric key cryptography, developed in the 1970s, revolutionized encryption by introducing a two-key system. This approach uses a public key, which can be freely shared like a mailing address, and a private key (also called a secret key), which must be kept confidential. The public key encrypts messages that only the corresponding private key can decrypt, enabling secure communication without the need to exchange secret keys beforehand. This innovation proved particularly transformative for digital currencies and blockchain technology. Digital currency systems implement elliptic curve cryptography, a specific form of asymmetric encryption. In cryptocurrency systems, users maintain self-custodial wallets containing both public keys for receiving funds and private keys for accessing and controlling their digital assets. This asymmetric approach eliminates the need for intermediaries while providing robust security and true ownership of digital currency through cryptography in computer networks.
Cryptography's Use Cases
Cryptography has become indispensable in modern digital life, enabling secure online transactions and communications across computer networks and the internet. When consumers make purchases on e-commerce platforms or access email accounts, cryptographic protocols work behind the scenes to protect their sensitive information from malicious actors. The technology ensures that credit card numbers, passwords, and personal data remain confidential during transmission over public networks.
The cryptocurrency revolution demonstrates cryptography's transformative potential beyond traditional applications. Digital currencies proved that asymmetric encryption could create secure, decentralized peer-to-peer payment systems operating without central authorities. The combination of public and private keys gives users complete custody of their funds, enabling them to control digital currency independently of banks or government agencies through cryptography in computer networks.
Blockchain technology has extended cryptocurrency's capabilities by introducing smart contracts—self-executing programs that automatically process inputs and outputs according to predetermined rules. These smart contracts leverage the security of asymmetric cryptography and the transparency of blockchain technology to create decentralized applications (dApps). Unlike traditional web applications controlled by corporations, dApps can operate without collecting personal user data such as passwords or email addresses. Instead, users authenticate by connecting their crypto wallets and signing transactions with their private keys. This innovation potentially reduces the amount of personal information individuals must share online, offering a new paradigm for digital privacy and security through cryptography in computer networks that continues to reshape how developers approach application design and user authentication.
Conclusion
Cryptography stands as a cornerstone technology protecting digital communications and transactions in the modern world. From its ancient origins in Caesar's military codes to today's sophisticated blockchain applications, cryptography has continuously evolved to address emerging security challenges. The fundamental principles of encryption and decryption, enabled by cryptographic keys, provide the foundation for secure online interactions that billions of people depend on daily across computer networks. The distinction between symmetric and asymmetric encryption methods offers different solutions for various security needs, with asymmetric cryptography proving particularly revolutionary in enabling decentralized systems. As digital threats grow more sophisticated and concerns about online privacy intensify, cryptography's role in computer networks becomes increasingly critical. The technology not only secures current digital infrastructure but also opens new possibilities for reimagining privacy, ownership, and trust in the digital age. Understanding cryptography in computer networks is essential for anyone seeking to comprehend how modern digital security works and how future innovations may continue to transform our relationship with technology and data privacy.
FAQ
What are the three types of cryptography?
The three types of cryptography are symmetric key cryptography, asymmetric key cryptography, and hash functions. Symmetric uses shared keys, asymmetric uses public-private key pairs, and hash functions create fixed-length digital fingerprints for data integrity verification.
How does cryptography work?
Cryptography uses mathematical algorithms to transform readable information into unreadable data, which can only be deciphered with a specific key. It ensures data privacy and security through encryption and hashing methods.
What are the 4 principles of cryptography?
The four principles of cryptography are confidentiality, integrity, non-repudiation, and authenticity. These ensure secure communication, data protection, and verification of identity and message origin.
Is cryptography hard to learn?
Cryptography requires dedication to master, but it's achievable with proper resources and structured learning. Start with foundational mathematics concepts, then progress to practical applications. Most learners benefit from formal courses and hands-on practice to build expertise effectively.

Cryptography: From Ancient Ciphers to Blockchain. The Complete Guide to Information Security in the Digital Age
Introduction to Cryptography: A Beginner's Guide
Understanding Merkle Proofs in Blockchain Technology
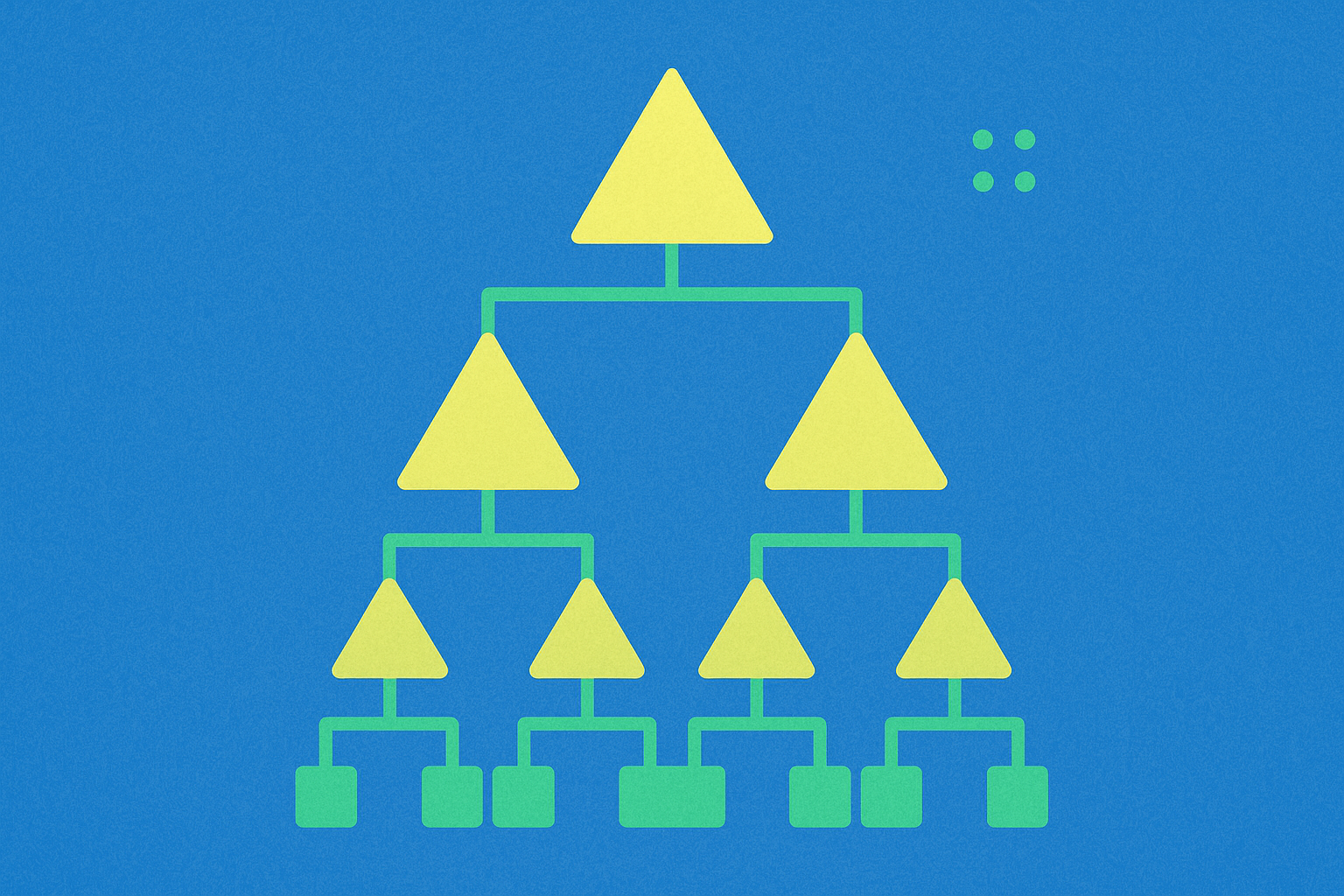
Understanding Merkle Tree Proofs in Blockchain Technology
Understanding Merkle Proofs in Blockchain Technology

Enhancing Security in Blockchain Networks with Cryptography Techniques
What is Fuel Network (FUEL)? Everything You Need to Know about FUEL

What Is BNB Chain?
All You Need To Know About Yescoin
How to Buy Baron ($BARRON) Coin: What is Baron Trump Cryptocurrency?

What Is AI Dev Agent (AIDEV)? No-Code Platform for Building Products